How LLMs Can Identify Anonymous Users at Scale: What Businesses Need to Know
LLMs can now identify anonymous users with 68% accuracy. Learn what businesses must do to protect user anonymity and mitigate deanonymization risks.

The End of Online Anonymity: LLMs Can Now Identify Users from Their Writing
Businesses that promise user anonymity face a new threat. Research from ETH Zurich and Anthropic demonstrates that large language models can identify anonymous users with up to 68% accuracy at 90% precision. What previously required hours of human investigation now takes minutes of automated processing.
Put simply: if your platform allows pseudonymous participation — from employee feedback systems to customer forums — that anonymity is no longer reliable.
Why This Matters for Your Business
Every platform handling anonymous data now carries elevated risk. According to research published on arXiv, LLMs can match users across platforms by analyzing just "a handful of comments." The attack costs $1-4 per attempt, making large-scale deanonymization economically viable for the first time.
Real numbers: When matching Hacker News profiles to LinkedIn accounts across 89,000 candidates, the LLM method achieved 45.1% recall at 99% precision — a 450-fold improvement over traditional methods. At internet scale with one million candidates, the system maintains approximately 35% recall at 90% precision.
For businesses, this translates to:
- Legal exposure under GDPR and CCPA for privacy breaches
- Trust erosion when anonymous feedback systems fail
- Competitive intelligence risks from employee discussions
- Platform abandonment by privacy-conscious users
How the Attack Works
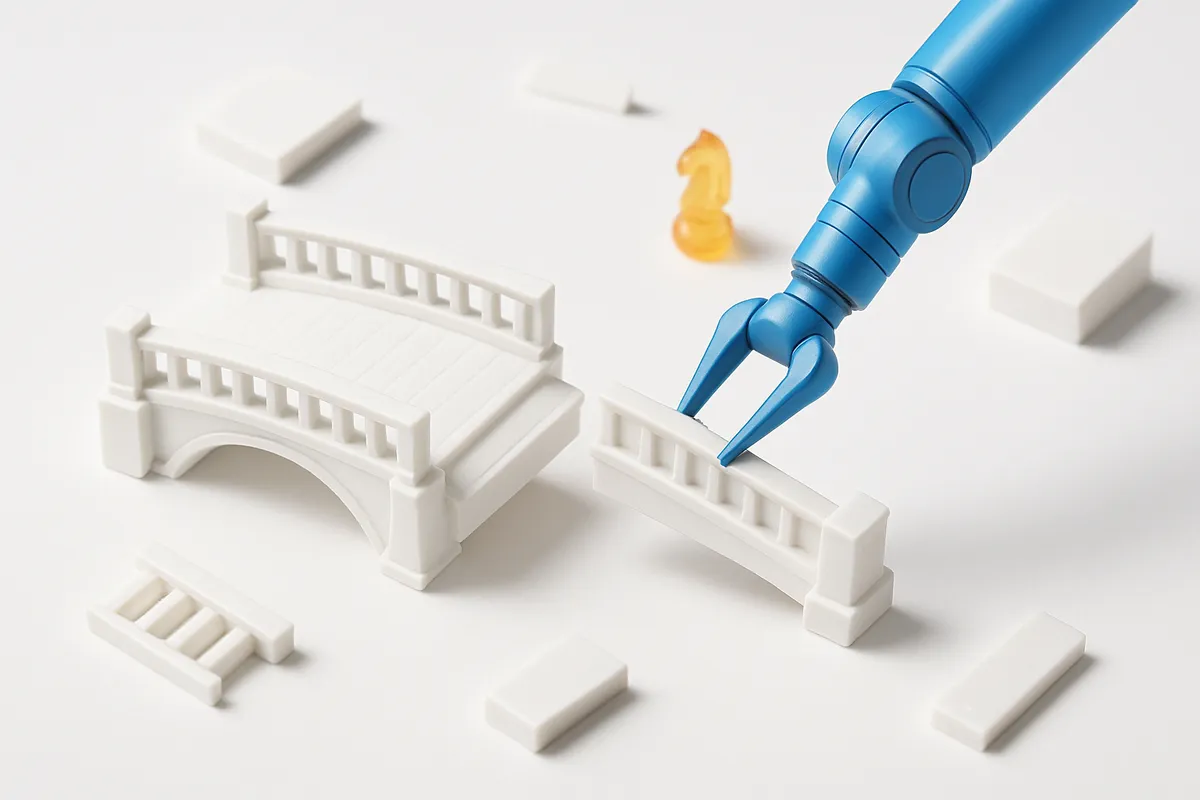
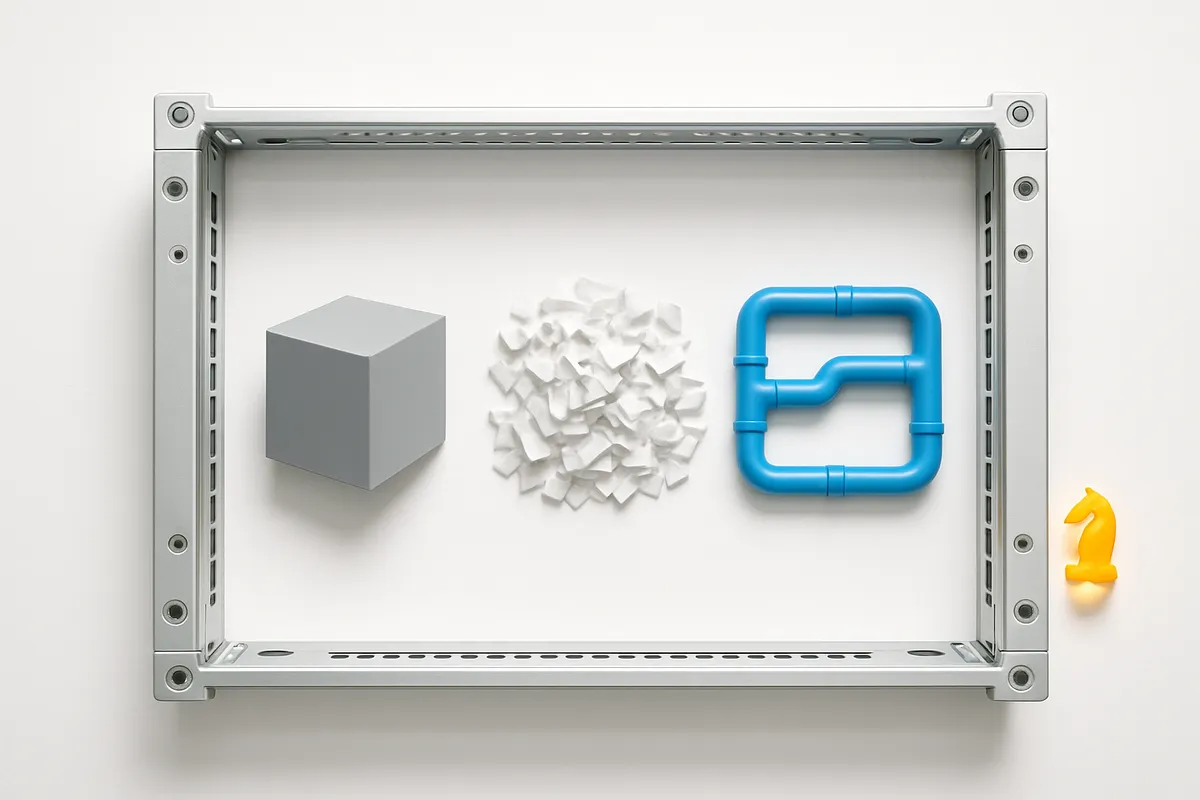
The deanonymization process uses a four-stage pipeline that appears benign to detection systems. As documented by Simon Lermen's research, the attack decomposes into seemingly innocent tasks:
- Extract: LLMs identify demographics, writing style, and interests from raw text
- Search: Features convert to semantic embeddings for efficient candidate matching
- Rank: LLMs reason over top candidates to verify matches
- Score: Final calibration reduces false positives
Honest take: The genius lies in the decomposition. Each step looks like legitimate data analysis — summarizing profiles, computing embeddings, ranking results. No single component triggers security alerts.
The system works directly on unstructured text across arbitrary platforms. Unlike the Netflix Prize deanonymization that required structured rating data, this approach needs only natural language content.
Real-World Impact We're Already Seeing
Researchers tested their system on actual anonymous data with concerning results:
- Anonymous interviews: Successfully identified 9 out of 33 scientist interviewees (27%) from publicly available transcripts with 82% precision
- Cross-platform matching: Linked Reddit users to their accounts on other platforms despite one-year gaps between posts
- Automated execution: The entire process runs autonomously with "minimal human oversight"
According to The Register's coverage, the automated approach replicates "in minutes what would take hours for a dedicated human investigator."
Your Options: Protection Strategies
Here's what we recommend based on the attack methodology:
1. Rate Limiting and Access Controls
The most effective short-term mitigation restricts data access:
- Enforce aggressive rate limits on user data APIs
- Detect and block automated scraping patterns
- Restrict bulk data exports to verified use cases
2. Data Minimization
Reduce the attack surface:
- Limit how much historical content remains publicly accessible
- Implement rolling deletions for sensitive anonymous content
- Separate internal identifiers from any public-facing data
3. Content Obfuscation
Make pattern matching harder:
- Add noise to timestamps and posting patterns
- Implement random delays in content visibility
- Break predictable behavioral signatures
4. Platform Architecture Changes
Long-term protection requires fundamental shifts:
- Move from pseudonymous to ephemeral identities
- Implement cryptographic solutions for verified anonymity
- Design systems that assume deanonymization attempts
The Hard Truth About Current Defenses
Traditional anonymization frameworks are "fundamentally inadequate" for this threat model, according to the research. Even LLM safety guardrails fail because:
- Open-source models can have protections removed entirely
- Refusals can be bypassed through task decomposition and "small prompt changes"
- The pipeline components resemble legitimate business analytics
What this means for your project: If you're relying on username changes, IP masking, or basic anonymization — you're not protected. The attack analyzes writing style, topic interests, and linguistic patterns that persist across identities.
Key Takeaway for Business
The era of "security through obscurity" for online anonymity has ended. LLMs have reduced the cost of deanonymization from hours of skilled investigation to minutes of automated processing at $1-4 per target.
Businesses must assume that any pseudonymous content can potentially be traced back to its author. This isn't a future risk — the DAS (De-Anonymization at Scale) framework already identifies same-author content "from pools of thousands at rates well above chance."
Here's what we recommend:
- Audit immediately: Identify all systems handling anonymous or pseudonymous data
- Implement rate limiting: Deploy access controls before broader architectural changes
- Update privacy policies: Inform users that absolute anonymity cannot be guaranteed
- Design for the new reality: Build future systems assuming deanonymization capabilities will only improve
The practical obscurity that once protected anonymous online participation no longer exists. Plan accordingly.