Fake Claude Code Install Pages Are Spreading Malware — What Your Team Needs to Know
Fake Claude Code install pages are spreading malware. Learn how attackers target developers, what to watch for, and how to protect your team from credential theft.
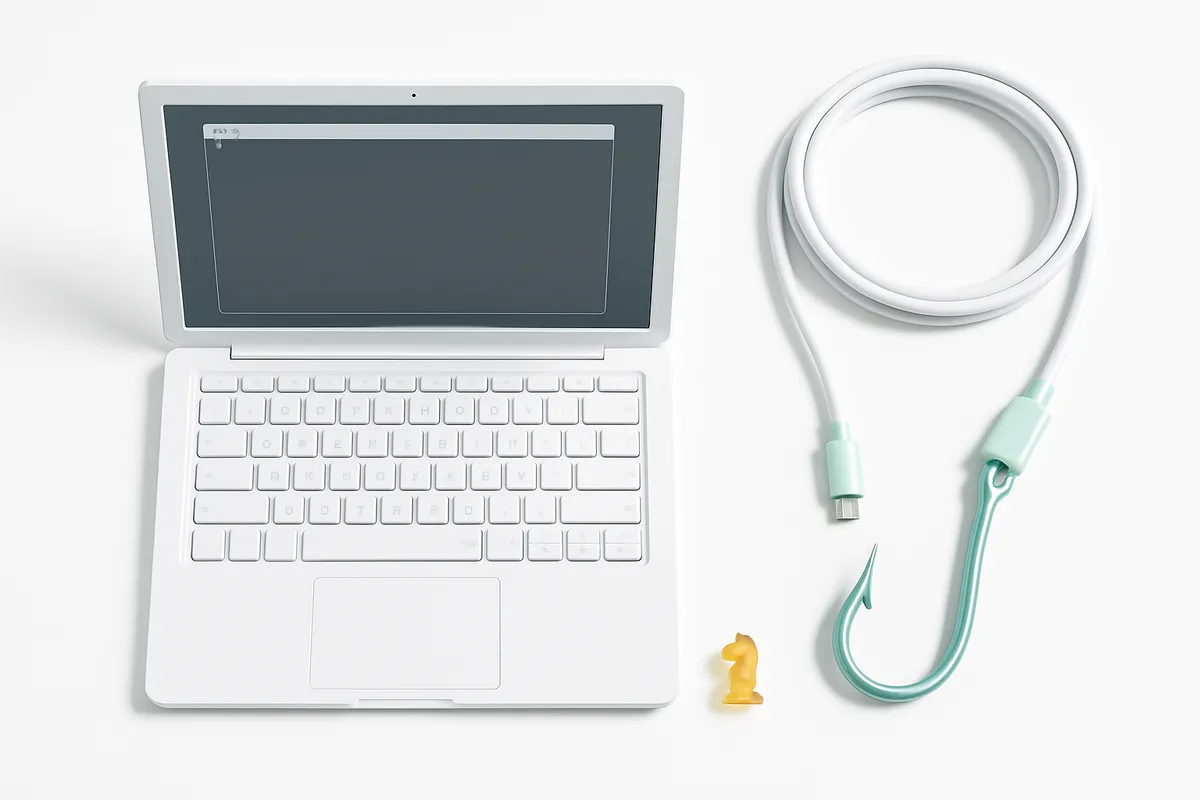
The Threat: Pixel-Perfect Fakes Targeting Developers
A developer searches "Claude Code install," clicks the top Google result, and follows the setup instructions. Everything looks right — the layout, the branding, even the documentation sidebar. Except the install command points to an attacker's server, and the developer just installed an infostealer instead of a coding assistant.
This is the core of the InstallFix campaign, a new malware distribution method documented by Push Security that exploits a simple reality: developers copy-paste install commands from official-looking pages every day, and almost nobody reads the full URL inside the command.
Why This Matters for Business
Developer machines are high-value targets. They hold SSH keys, API tokens, cloud credentials, database access, and often have elevated permissions across internal systems. A single compromised developer workstation can give attackers a foothold into production infrastructure, CI/CD pipelines, and customer data.
The InstallFix technique is particularly dangerous because it requires no exploit, no vulnerability, and no file download in the traditional sense. The victim runs a command willingly, believing it to be legitimate. This bypasses most endpoint protections that look for suspicious downloads or unsigned executables.
Honest take: the traditional security model for CLI tools boils down to "trust the domain." As Push Security notes, that model breaks completely when attackers can place convincing clones at the top of search results through paid ads.
How the InstallFix Attack Works
Step 1: Malvertising via Google Ads
The fake Claude Code pages are distributed exclusively through sponsored search results on Google. Searches like "Claude Code install" or "Claude Code CLI" surface the malicious pages above or alongside legitimate results. According to Push Security, four out of five ClickFix lures are now distributed via search engines.
Step 2: Near-Identical Clone Pages
The cloned pages are virtually pixel-perfect copies of the official Claude Code installation page. Same layout, same branding, same documentation sidebar. The only difference sits inside the install commands for macOS (shell) and Windows (PowerShell/Command Prompt) — they point to an attacker-controlled endpoint instead of claude.ai.
All other links on the fake page redirect to the legitimate Anthropic site. As BleepingComputer reports, "a victim that lands on the page and follows the fake instructions could continue normally without realizing anything had gone wrong."
Step 3: Malware Execution
On Windows, the malicious command launches mshta.exe to fetch and execute a remote HTA file containing embedded malicious scripts. According to Cyber Security News, the payload executes entirely in memory — no standalone file lands on disk, making forensic recovery significantly harder.
Step 4: Redirect to the Real Site
After executing the malicious command, victims are redirected to the legitimate Claude Code page. This removes suspicion entirely — the developer assumes the install worked and moves on, unaware that malware is now running on their machine.
The Payload: Amatera Infostealer
The final payload is Amatera Stealer, a relatively new malware family that Proofpoint identifies as a rebranded and improved version of ACR Stealer. It operates as a Malware-as-a-Service (MaaS) product, sold on a subscription basis to cybercriminals.
What Amatera steals:
- Passwords stored in web browsers
- Cookies and session tokens (which can bypass MFA)
- Crypto wallet data
- System information and installed software details
- Any files matching configurable search patterns
Real numbers: Amatera communicates with command-and-control servers using hardcoded IP addresses of legitimate CDNs, which makes network-level detection difficult. According to Blackpoint Cyber's analysis, the malware performs socket operations through low-level Windows syscalls (NtDeviceIoControl), bypassing standard networking libraries that EDR tools typically monitor.
Put simply: Amatera is designed from the ground up to avoid detection — it skips the standard Windows APIs that security tools watch, talks to servers that look like legitimate CDN traffic, and runs its core functions in memory.
This Is Part of a Larger Pattern
The Claude Code clone is not an isolated incident. Push Security documented a broader trend of developer tools being targeted:
- Fake Homebrew installation pages delivering the Cuckoo infostealer to macOS users, using the same "copy this install command" approach
- Trojanized npm packages mimicking Claude Code's official npm package name, targeting developers who make a typo or trust an unofficial source
- Fake OpenClaw installers on GitHub boosted by Bing's AI search results, delivering infostealers and GhostSocks proxy malware
- Fake Claude artifacts on the claude.ai domain itself (user-generated content inheriting the domain's trust), promoted via hijacked Google Ads and viewed over 15,000 times before removal
The common thread: attackers are following developers to the tools they use daily and exploiting the trust built into installation workflows.
What This Means for Your Project
For Individual Developers
- Never copy install commands from search ad results. Go directly to the official documentation by typing the URL manually or using a bookmark
- Read the URL inside every install command before running it. The malicious commands look identical except for the domain they fetch from
- Be suspicious of redirects. If a page sends you to the real site after you run a command, that does not validate the original page was legitimate
For Engineering Teams
- Block sponsored search results through browser extensions or DNS-level filtering where possible
- Restrict PowerShell and mshta.exe execution on developer machines via Group Policy. As Blackpoint Cyber recommends, restrict access to the Windows Run dialog and remove App-V components where not required
- Enable comprehensive PowerShell logging and monitor for suspicious process chains like
explorer.exe → wscript.exe → powershell.exe - Use EDR tools that detect behavior-based anomalies, not just signature-based threats. Amatera specifically avoids standard API hooks that many tools rely on
- Enforce browser credential separation — prevent password synchronization between personal and corporate browser profiles. Stolen session cookies from a developer's browser can bypass MFA entirely
If a Machine Is Already Compromised
According to Hadrian's remediation guide, the response should follow this order:
- Revoke all sessions and tokens immediately — not just passwords, but active sessions
- Investigate for abuse — check if the attacker used stolen credentials to access internal systems or establish persistence
- Clean or reimage the device — do not restore from recent backups unless you are certain they are clean
- Reset all passwords and enforce MFA re-enrollment on a verified clean device
Key takeaway for business: speed matters. Infostealers exfiltrate data within minutes. Every hour between compromise and response is an hour the attacker has to use stolen credentials.
Here Is What We Recommend
For teams of any size, three changes reduce exposure significantly:
Bookmark your tool installation pages. A five-second habit eliminates the primary attack vector entirely. Never trust search results for install commands — not even the top organic result, and especially not ads.
Treat install commands like code reviews. Before running any command from a web page, verify the domain it connects to. A quick
curl -vor reading the URL in the command takes seconds and would have caught every variant in this campaign.Assume breach for stolen sessions. If any developer machine is compromised, invalidate every session token and API key that machine had access to. Password resets alone are insufficient when attackers have session cookies — those cookies bypass MFA.
Honest take: this attack succeeds not because of technical sophistication but because of workflow trust. Developers run install commands dozens of times a week. The fix is not a new tool — it is a habit change. Verify the source, read the command, and never trust a search ad for software installation.
Frequently Asked Questions
How can I verify the installation command is from the official Claude Code source instead of a malicious clone?
Check the URL manually: official Claude Code instructions come from docs on anthropic.com or claude.ai, and the npm install command references the official @anthropic-ai/claude-code package. If the install command points to any other domain — especially a .pages.dev, random subdomain, or unfamiliar server — do not run it. Always navigate to the official site directly rather than through search results.
What specific system data does the Amatera infostealer collect beyond passwords and cookies?
According to Proofpoint's analysis, Amatera uses configurable glob-syntax file search patterns to find and exfiltrate data from browsers, crypto wallets, and other software. It also collects system information and can download and execute secondary payloads, meaning the initial infection can lead to additional malware being installed.
Why do attackers use legitimate CDN services like Cloudflare Pages and Squarespace to host malicious content?
Legitimate hosting platforms provide trusted SSL certificates, high availability, and domain reputations that pass most security filters. A page hosted on Cloudflare Pages (.pages.dev) or Squarespace looks normal to both users and automated security tools, making it significantly harder to detect or block without inspecting the actual content being served.
Can I still be infected if I get redirected to the real Claude Code site after visiting a fake installation page?
Yes. The redirect happens after the malicious command has already been executed. The redirect to the legitimate site is a deliberate design choice — it removes suspicion so the victim does not investigate further. If you ran the install command before being redirected, the malware is already active on your machine.
How does checking the URL in the command prevent falling victim to these fake installation guides?
The malicious install commands are identical to legitimate ones except for the server URL they connect to. Instead of fetching from claude.ai or the official npm registry, they fetch from attacker-controlled domains. Reading the full command before running it — specifically the domain or IP address it connects to — is the single most effective way to catch the deception.
This article is based on publicly available sources and may contain inaccuracies.


