The Rise of Malicious Repositories on GitHub: What Development Teams Need to Know
Discover how malicious GitHub repositories threaten supply chains. Learn typosquatting tactics, credential theft risks, and essential security practices for dev teams.

Why GitHub Has Become a Prime Target for Supply Chain Attacks
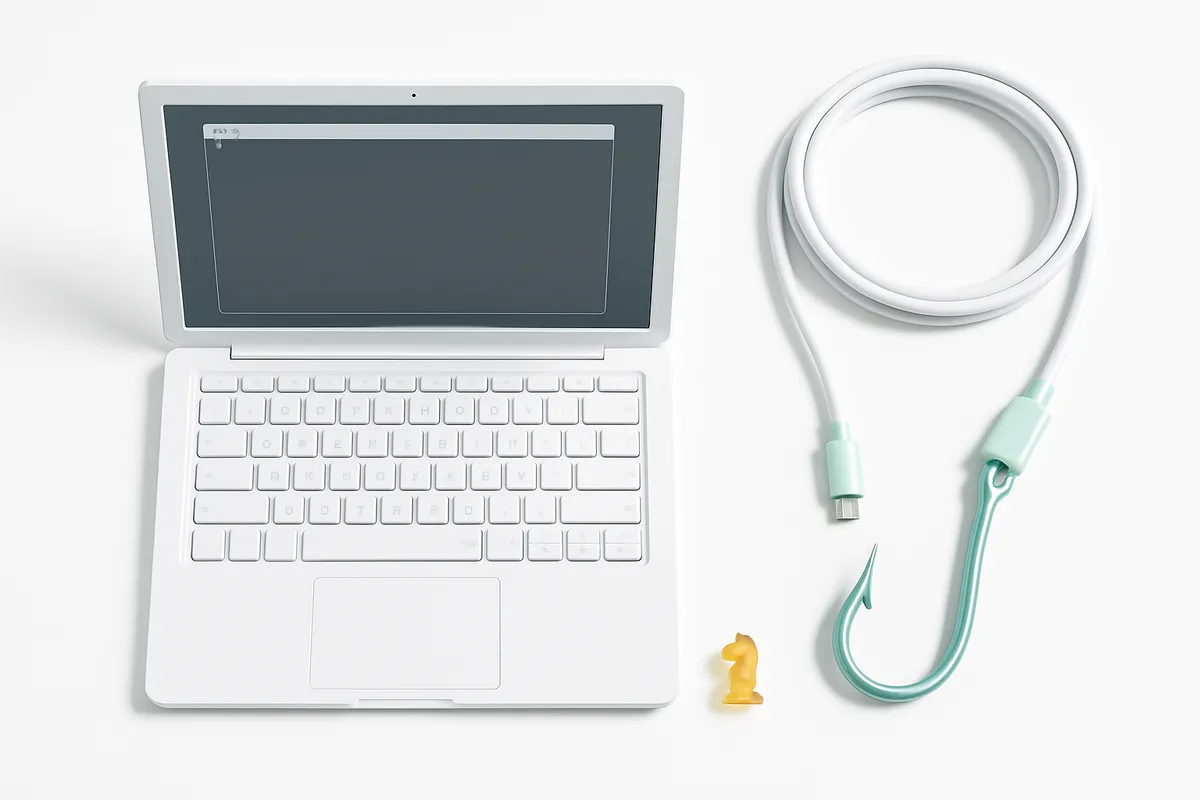
A developer clones a repository that looks exactly like a popular open-source library. The README is polished, the code appears functional, and the star count seems reasonable. Weeks later, credentials start leaking from the CI/CD pipeline. The repository was a carefully crafted fake.
This scenario is no longer rare. GitHub, as the largest platform for open-source software, has become a persistent target for threat actors who publish malicious repositories designed to compromise developer environments, steal credentials, and inject backdoors into production systems. For any business that depends on open-source code — which is nearly every software company — this is a direct operational risk.
How Attackers Exploit GitHub's Trust Model
Typosquatting and Copycat Repositories
The simplest technique is also the most effective. Attackers create repositories with names nearly identical to popular libraries — swapping a letter, adding a hyphen, or using a similar-sounding name. According to Snyk's analysis, these GitHub malware repositories pose a threat not just to individual developers but to entire organizations. When cloned or incorporated into other projects, the malware spreads, leading to potential data breaches or system compromises.
Put simply: if a developer types react-routter instead of react-router and finds a repository that looks legitimate, one careless clone can compromise an entire build pipeline.
RepoJacking: Hijacking Abandoned Namespaces
A more sophisticated attack involves taking over retired GitHub usernames or organization names and republishing trojanized versions of previously legitimate repositories. Research by AquaSec's "Nautilus" team found that approximately 2.95% of analyzed repositories could be vulnerable to RepoJacking — extrapolated across GitHub, that puts roughly 9 million projects at potential risk.
This matters because existing projects that reference the original repository URL will silently pull from the attacker's version after a takeover. Submodule updates, Terraform modules, CI/CD workflows — any automated reference becomes a potential infection vector.
Invisible Code Attacks
The latest evolution is particularly dangerous. Aikido Security researchers reported in March 2026 finding 151 malicious packages uploaded to GitHub in a single week (March 3–9), using unicode characters invisible to human eyes, editors, and code review interfaces. The visible portions of these packages were high quality. The malicious payloads — credential stealers, token harvesters — were encoded in characters that simply don't render on screen.
Honest take: when the malicious code is literally invisible, manual code review is no longer a sufficient defense.
The Business Impact Is Concrete, Not Theoretical
The tj-actions/changed-files Incident
In one of the most significant supply chain compromises tracked as CVE-2025-30066, attackers modified a GitHub Action used in over 23,000 repositories. The injected code — a base64-encoded Node.js function — downloaded a malicious Python script that scanned GitHub Runner memory for secrets like passwords and API keys. Researchers from Wiz identified dozens of affected repositories run by large organizations.
Real numbers: 23,000 repositories exposed. One compromised Action. Secrets from public repositories dumped into publicly readable workflow logs.
The Shai-Hulud Campaign
As documented in GitHub's own security blog, the multi-wave Shai-Hulud malware campaign spread through compromised npm packages by scavenging local system tokens during installation. The stolen tokens were then used to propagate further — and some tokens were hoarded for weeks or months before being used in follow-up attacks. One compromised maintainer account could cascade into hundreds of infected packages.
The Expanding Attack Surface
Research from OX Security published by Dark Reading mapped 10 distinct risk vectors across the software development lifecycle where GitHub references create entry points for malicious code. The numbers are telling:
- Infrastructure-as-Code: approximately 114,000 Terraform files and 13,000 terragrunt.hcl files reference GitHub modules, many using mutable references like
?ref=main - Configuration management: roughly 3,000 Ansible requirements files, 5,000 Grafana installations, and 5,000 Logstash configurations pull components directly from GitHub
- Helm charts: unverified charts with GitHub-sourced hooks can deploy malicious resources with cluster-level permissions
What this means for your project: the attack surface extends far beyond npm install. Any automated reference to a GitHub URL — in Terraform, Ansible, Docker, Helm, or CI/CD configs — is a potential vector.
Why Attackers Are Moving From Package Registries to Repositories
According to ReversingLabs research covered by Dark Reading, malicious package attacks on registries like npm and PyPI have actually been declining. Package registries have invested heavily in automated scanning, malware detection, and account security. The result: threat actors are shifting to GitHub repositories, where defenses are less mature.
Repositories require more manual interaction — finding, cloning, reviewing, integrating — which theoretically makes them harder to exploit. But attackers compensate with higher-quality fakes, SEO manipulation to appear in search results, and techniques like invisible code that bypass review entirely.
Key takeaway for business: stronger package registry defenses pushed attackers upstream in the supply chain. The problem didn't shrink — it moved.
Practical Defenses That Actually Work
1. Lock Everything Down With Immutable References
Never reference GitHub content using mutable branch names like main or master. Pin dependencies, submodules, Actions, and IaC modules to specific commit SHAs.
For GitHub Actions, this means using:
uses: actions/checkout@a1b2c3d4e5f6 (commit SHA)
instead of:
uses: actions/checkout@v4 (mutable tag)
2. Automate Dependency Scanning in CI/CD
As recommended by supply chain security practitioners, every pull request that modifies dependencies should trigger automated checks:
- Lockfile consistency validation (use
--frozen-lockfileor--immutableflags) - Cross-referencing against the GitHub Advisory Database and OSSF malicious packages feed
- Static analysis for suspicious patterns like typosquatting or unusual install scripts
Tools like DataDog's GuardDog and the RoguePkg GitHub Action can automate malicious package detection directly in the PR workflow, blocking merges when threats are identified.
3. Control Update Timing
Malicious packages are most dangerous right after publication — before the community detects and reports them. Configure Dependabot or Renovate with cooldown periods so automatic updates don't pull in freshly published (and potentially compromised) versions immediately.
4. Verify Repository Authenticity Before Cloning
Before integrating any GitHub repository:
- Check the organization or user account age and history
- Verify the repository URL matches official documentation exactly
- Look for recent ownership changes (a sign of potential RepoJacking)
- Compare the repository content against known-good versions using tools like AST comparison
5. Protect Maintainer Accounts
GitHub's post-mortem advice after the Shai-Hulud campaign emphasized maintainer account security: enable two-factor authentication with passkeys, use fine-grained personal access tokens with minimal permissions, and regularly audit which tokens have repository access.
Here is what we recommend as a minimum security baseline for any team using open-source dependencies:
- Pin all external references to commit SHAs — Actions, submodules, Terraform modules, Helm charts
- Run automated malware scanning on every PR that touches dependency files
- Enforce lockfile integrity in CI with
--frozen-lockfile - Delay automatic dependency updates by 48–72 hours
- Require passkey-based 2FA for all accounts that publish packages or maintain repositories
The Honest Assessment
Supply chain attacks through GitHub repositories are not going away. The GitHub security team acknowledges that adversaries "learn quickly, target maintainer workflows, and exploit trust boundaries in publication pipelines." As Snyk notes, this type of attack is not limited to GitHub — any source code repository where code can be shared and copied is a potential vector.
Honest take: the solution is not to stop using open source. That would mean abandoning the biggest advantage modern development has. The solution is to treat every external dependency — whether from npm, PyPI, or a GitHub repository — as untrusted input until verified.
Key takeaway for business: the cost of implementing automated dependency scanning, pinning references, and enforcing lockfile integrity is measured in hours of DevOps setup. The cost of a supply chain compromise — leaked credentials, breached production systems, incident response — is measured in weeks and significant financial damage. The math is straightforward.
Frequently Asked Questions
How can developers distinguish between legitimate repositories and convincing fakes that mimic popular projects?
Verify the repository URL against the project's official documentation or website. Check account age, contribution history, and whether the organization is verified on GitHub. Fakes often have recent creation dates, thin commit histories, and no linked CI/CD status badges from recognized services.
Can attackers successfully take over retired GitHub accounts and organizations to publish trojanized versions of previously legitimate projects?
Yes. AquaSec's research found that approximately 2.95% of analyzed repositories could be vulnerable to RepoJacking, where attackers register retired usernames and republish trojanized code. GitHub has implemented some protections against this, but the risk remains significant for projects referencing old URLs.
How effective are current trust signals like star counts, fork numbers, and commit history at identifying malicious repositories?
They are unreliable. Stars and forks can be artificially inflated, and commit history can be fabricated. These signals should be treated as supplementary information, not proof of legitimacy. Automated scanning against known malware databases is significantly more effective than visual trust indicators.
What techniques do attackers use to keep malicious repositories active and visible in GitHub search results?
Attackers use SEO-style techniques: popular keywords in repository names and descriptions, fabricated stars and forks, frequent commits to appear active, and high-quality README files. The most recent evolution uses invisible unicode characters to hide malicious payloads from code review, making the visible code appear clean and functional.
This article is based on publicly available sources and may contain inaccuracies.